As cybersecurity threats continue to evolve, the role of a SOC Analyst is also changing. In 2026, SOC teams are expected to handle a large volume of alerts, logs, endpoints, and constantly changing attack techniques. The Security Operations Center (SOC) acts as the first line of defense, and the tools used by SOC analysts play a major role in detecting, investigating, and responding to security incidents.
In many SOCs I’ve seen, analysts struggle not because they lack skills, but because they don’t fully understand how to use the tools available to them. When the right tools are used properly, daily SOC work becomes far more manageable and effective.
For anyone working in a SOC or planning to move into this role, understanding the right tools is extremely important. These tools help analysts manage daily workloads, investigate incidents confidently, and respond to threats on time.
In this article, I will walk you through the top 10 cybersecurity tools every SOC analyst should know in 2026, explained in simple and practical terms.
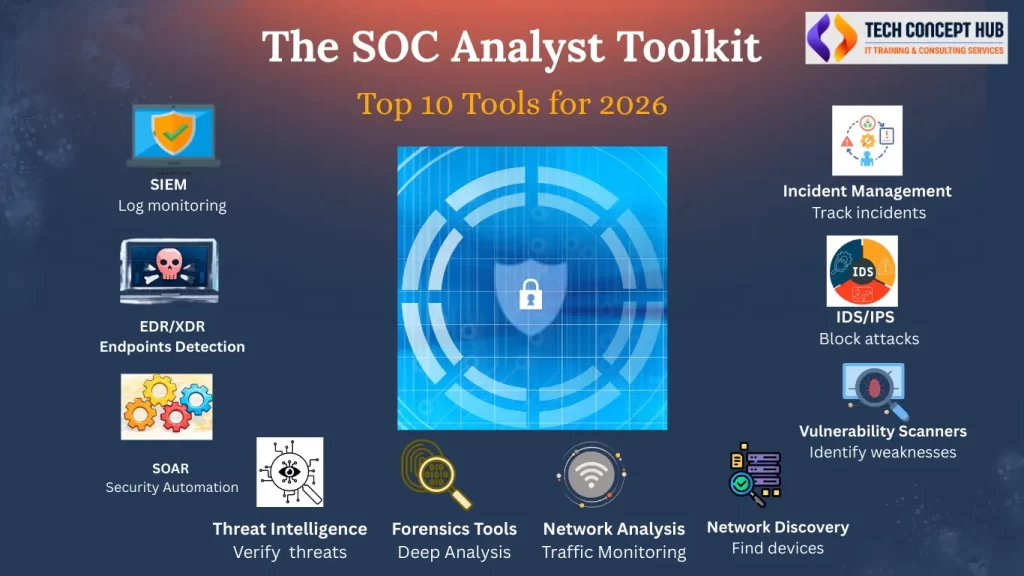
SIEM (Security Information & Event Management)
SIEM is the tool SOC analysts spend most of their time working with. It collects logs from firewalls, servers, endpoints, applications, and cloud platforms and brings everything into one place. When an alert is triggered, the first step for an analyst is usually to check the SIEM to understand what happened, when it started, and which systems are involved. By searching logs and connecting related events, analysts can gradually build the full picture of an incident. In many SOCs I’ve seen, almost every investigation starts in the SIEM, which is why being comfortable with alerts and basic searches is essential for any SOC analyst.
Examples: Splunk, Microsoft Sentinel (very common in 2026), Elastic SIEM, IBM QRadar
EDR / XDR (Endpoint Detection & Response / Extended Detection & Response)
From my experience, most real-world attacks are first visible on endpoints like laptops and servers. EDR tools continuously monitor what is happening on these systems and help SOC analysts spot suspicious behavior such as unusual processes, unknown files, or unexpected system changes. XDR builds on this by combining endpoint data with signals from network, email, and cloud sources, giving a much clearer picture of an attack. During incidents, endpoint alerts often provide the strongest evidence of compromise and allow analysts to quickly investigate and isolate affected systems before the issue spreads further.
Examples: CrowdStrike Falcon, Microsoft Defender for Endpoint, SentinelOne, Cortex XDR, Sophos Intercept X
SOAR (Security Orchestration, Automation, and Response)
In mature SOCs, handling alerts manually does not scale, and this is where SOAR becomes important. SOAR platforms help teams automate routine response actions using predefined playbooks. Tasks such as blocking an IP, disabling a user account, or isolating an endpoint can be handled automatically once certain conditions are met. Analysts still stay in control, but SOAR removes a lot of repetitive work and allows them to focus on deeper investigations instead of operational tasks.
Examples: Palo Alto Cortex XSOAR, Splunk SOAR, IBM Resilient, Swimlane
Threat Intelligence Platforms (TIPs)
Threat intelligence plays a key role in separating real threats from noise. Instead of treating every alert as critical, SOC analysts use threat intelligence to check whether indicators like IP addresses, domains, file hashes, or malware are already known and active in the wild. This context helps analysts prioritize incidents and avoid wasting time on false positives. In day-to-day SOC work, threat intelligence is often used to validate attacks and support investigation decisions.
Examples: MISP, Recorded Future, Anomali, ThreatConnect, VirusTotal
Endpoint Forensics Tools (Windows)
When an incident escalates, logs alone are often not enough. Endpoint forensics tools allow analysts to examine a Windows system in detail and understand what actually happened on the host. These tools help review running processes, startup programs, file activity, and registry changes. They are especially useful during malware and ransomware investigations, where understanding attacker behavior is critical. Even basic knowledge of Windows internals can significantly improve investigation quality.
Examples: Microsoft Sysinternals Suite (Process Explorer, Autoruns)
Network Analysis & Packet Capture Tools
Not every attack leaves clear traces in logs or alerts. In many cases, network traffic analysis is required to see what is really going on. Packet capture and network analysis tools allow SOC analysts to observe how systems communicate with internal and external destinations. By analyzing this traffic, analysts can identify suspicious connections, command-and-control communication, or data exfiltration. Once you understand normal network behavior, detecting anomalies becomes much easier.
Examples: Wireshark, tcpdump, Zeek (Bro), NetworkMiner
Network Discovery Tools
Network discovery tools help SOC teams understand what is actually present in their environment. These tools scan the network to identify systems, open ports, and running services, including devices that may not be properly tracked or managed. Unknown or unmanaged systems often create security blind spots and become easy targets for attackers. In many SOCs, network discovery is used both during investigations and as part of ongoing security hygiene.
Examples: Nmap, Angry IP Scanner, SolarWinds Network Discovery, Lansweeper
- Vulnerability Scanners (Nessus, OpenVAS)
Vulnerability scanners are used to identify weaknesses before attackers exploit them. They scan systems to detect missing patches, insecure configurations, and known vulnerabilities. SOC analysts review scan results to understand risk levels and help prioritize remediation efforts. While these tools do not directly stop attacks, they play an important role in reducing the organization’s overall exposure and preventing incidents before they occur.
Examples: Nessus, OpenVAS, Qualys VM, Rapid7 InsightVM
IDS / IPS (Intrusion Detection & Prevention Systems)
IDS and IPS tools monitor network traffic to identify known attack patterns and suspicious activity. An IDS generates alerts for further investigation, while an IPS can actively block malicious traffic. SOC analysts regularly review these alerts to determine whether they represent real threats or false positives. These tools are especially useful for detecting network-based attacks that may bypass endpoint or application-level defenses.
Examples: Snort, Suricata, Palo Alto Threat Prevention, Cisco Firepower
Incident Management & Threat Sharing Tools
Security incidents are not only about technical analysis; they also require proper coordination and documentation. Incident management tools help SOC teams track incidents from start to closure, assign tasks, and record actions taken during investigations. This structured approach ensures nothing is missed and helps teams improve their response over time. Threat sharing platforms further strengthen security by allowing organizations to exchange indicators and learn from attacks seen by others.
Examples: ServiceNow Security Operations, Jira, TheHive, MISP
Final Thoughts (Including AI & Agentic SOC)
In 2026, a SOC analyst is not expected to master every tool in the environment. What really matters is understanding how different tools come together during an investigation. SIEM, EDR, SOAR, and threat intelligence are the backbone of most SOCs today, and these are the platforms analysts work with on a daily basis.
One clear change I’ve seen over the years is the growing use of AI and automation inside SOC tools. AI is mainly being used to reduce alert noise, help with prioritization, and assist with basic investigation steps. This makes day-to-day SOC work more manageable, especially when teams are dealing with a high volume of alerts. Some platforms are now moving toward more agent-based approaches, where AI can pull data from multiple tools and suggest response actions.
This does not replace SOC analysts. In reality, it helps them spend less time on repetitive tasks and more time focusing on real security incidents. For anyone entering a SOC role, the approach is simple: build strong fundamentals in security, logging, and investigations first. Once the basics are clear, AI-driven tools become a powerful support rather than a black box. SOC analysts who understand both will be far more effective in the years ahead.
Cybersecurity Course Syllabus:
https://techconcepthub.com/cybersecurity-course-syllabus/
Thank You!