If you are trying to break into cybersecurity, the advice can feel confusing and, honestly, discouraging. One person tells you to learn Python. Another says you need cloud, threat hunting, malware analysis, and five certifications before anyone will even look at your resume. For people coming from non-IT backgrounds, it can feel impossible.
That is exactly why the SOC analyst role still matters in 2026.
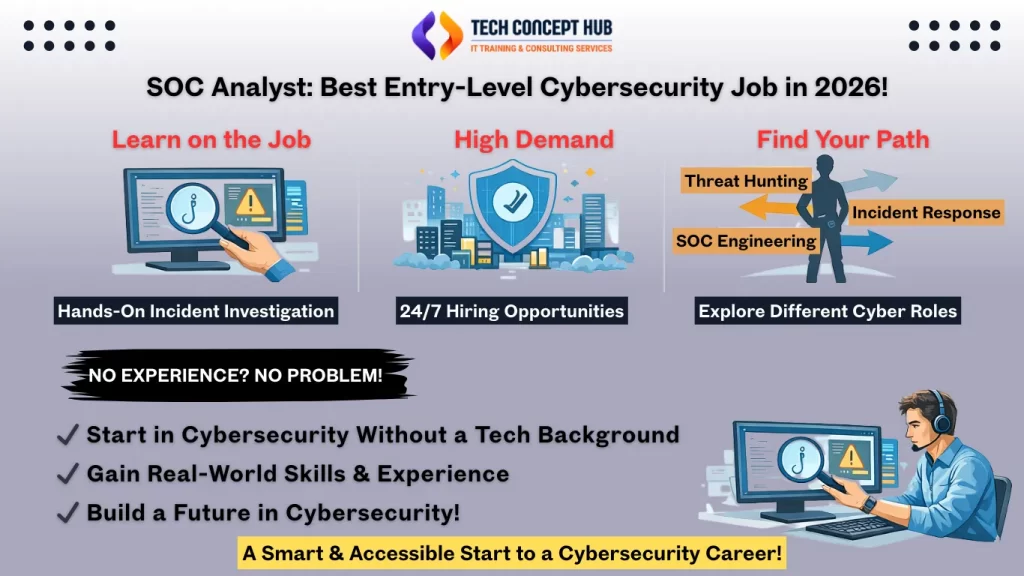
Despite all the noise around “advanced” cybersecurity careers, SOC remains one of the few roles where beginners can realistically get hired, learn on the job, and build real experience without pretending to be an expert on day one.
SOC Is Actually the best option to get job in cybersecurity for freshers
There is a common myth that SOC analysts need to be elite hackers or strong programmers. That is not what entry-level SOC work looks like in real life.
Most Tier 1 SOC analysts are not writing exploits or reversing malware all day. They are monitoring alerts, reviewing logs, validating whether something is real or just noise, and escalating incidents when needed. For that, you need solid fundamentals of networking basics, how common attacks work, what “normal” activity looks like and not years of experience.
I have personally seen people move into SOC roles from help desk, networking, QA, and even completely non-technical backgrounds. What mattered most was not their resume; it was their curiosity, consistency, and willingness to sit with problems they did not immediately understand.
That mindset matters far more than knowing every tool upfront.
You Learn Faster Because You are Dealing With Real Incidents
One of the biggest advantages of working in a SOC is that learning is not theoretical. You are not just reading about attacks, you’re seeing them happen.
On a normal shift, you might investigate a phishing alert, look into a suspicious login, or analyze endpoint behavior that does not quite make sense. Some alerts will be false positives. Others will not. That process teaches you how attackers actually behave, how detection tools really work, and how messy real-world security can be.
No course or lab fully prepares you for that. SOC work does.
SOC Hiring Is not Slowing Down Anytime Soon
Security monitoring isn’t optional anymore. Companies might delay projects, cut tools, or freeze hiring elsewhere, but they still need people watching their environment.
Banks, hospitals, retailers, SaaS companies, governments, they all either run their own SOC or outsource to a managed SOC provider. And because SOCs operate 24/7, they constantly need people across shifts. There’s also steady turnover, because many analysts treat SOC as a stepping stone rather than a final destination.
That combination creates regular openings, especially for junior roles. Compared to more specialized cybersecurity positions, SOC is simply more accessible.
SOC Gives You Clarity About Your Career Direction
A lot of beginners do not actually know what they want to specialize in and that is normal. SOC work exposes you to many parts of cybersecurity at once.
Over time, you start noticing patterns:
- Maybe you enjoy digging deep into incidents
- Maybe threat hunting excites you more than alert triage
- Maybe you’re more interested in tools and automation than investigations
Many professionals use SOC as a base before moving into roles like incident response, threat hunting, digital forensics, malware analysis, SOC engineering, or even leadership. The experience translates well because you understand how security operations actually function day to day.
Why SOC Is Easier to Enter Than Other Cybersecurity Roles
There are practical reasons SOC remains one of the easiest entry points:
- Shift work creates frequent openings (especially nights or rotations)
- SOC roles often have higher turnover by design
- Regulations sometimes require SOC work to stay local
- Companies prefer to train juniors rather than overpay for seniors
None of this makes SOC work “easy,” but it does make it attainable.
A Realistic SOC Career Path
Most SOC careers follow a rough progression, even if the titles vary:
- Tier 1 SOC Analyst: Alert monitoring, basic investigation, identifying false positives, escalating real incidents
- Tier 2 / Incident Responder: Deeper investigations, containment, coordination with IT and security teams
- Tier 3 / Threat Hunter: Proactive hunting, advanced analysis, improving detections
- SOC Engineer: Building and optimizing SIEM, EDR, SOAR, automation, and workflows
- SOC Lead / Manager: Running operations, mentoring analysts, handling escalations, reporting to leadership
Not everyone follows the same path, and that’s okay. Some people move into cloud security, forensics, or threat intelligence once they figure out what they enjoy most.
In Summary
SOC work is not glamorous. There will be repetitive alerts, stressful incidents, and shifts that test your patience. But it’s also one of the most honest ways to enter cybersecurity.
You get paid to learn. You gain real experience. And you build a foundation that opens doors later.
In 2026, for anyone serious about starting a cybersecurity career, especially beginners, SOC analyst is still one of the smartest and most realistic places to begin.